Secure DMZ Hosting
Example of Preliminary On-Premises Architecture Proposal
- Audience: Executives, managers, non-technical stakeholders
- Goal: Explain value, risk control, cost, and security in clear language.
1. Executive Summary
We propose hosting the system on physical servers within the company’s infrastructure using a secure DMZ (Demilitarized Zone) architecture. This ensures data sovereignty, security control, and independence from external cloud providers.
2. Why On-Premises?
Explain in business terms:
- Full control of data
- No dependency on third-party cloud providers
- Compliance with internal policies
- Long-term cost predictability
- Increased trust for sensitive inspection data
3. What is a DMZ
Simple Non-technical explanation:
A DMZ is a secure buffer zone between the Internet and the internal company network. It ensures that even if an external attack occurs, internal systems remain protected.
Include a very simple visual diagram.
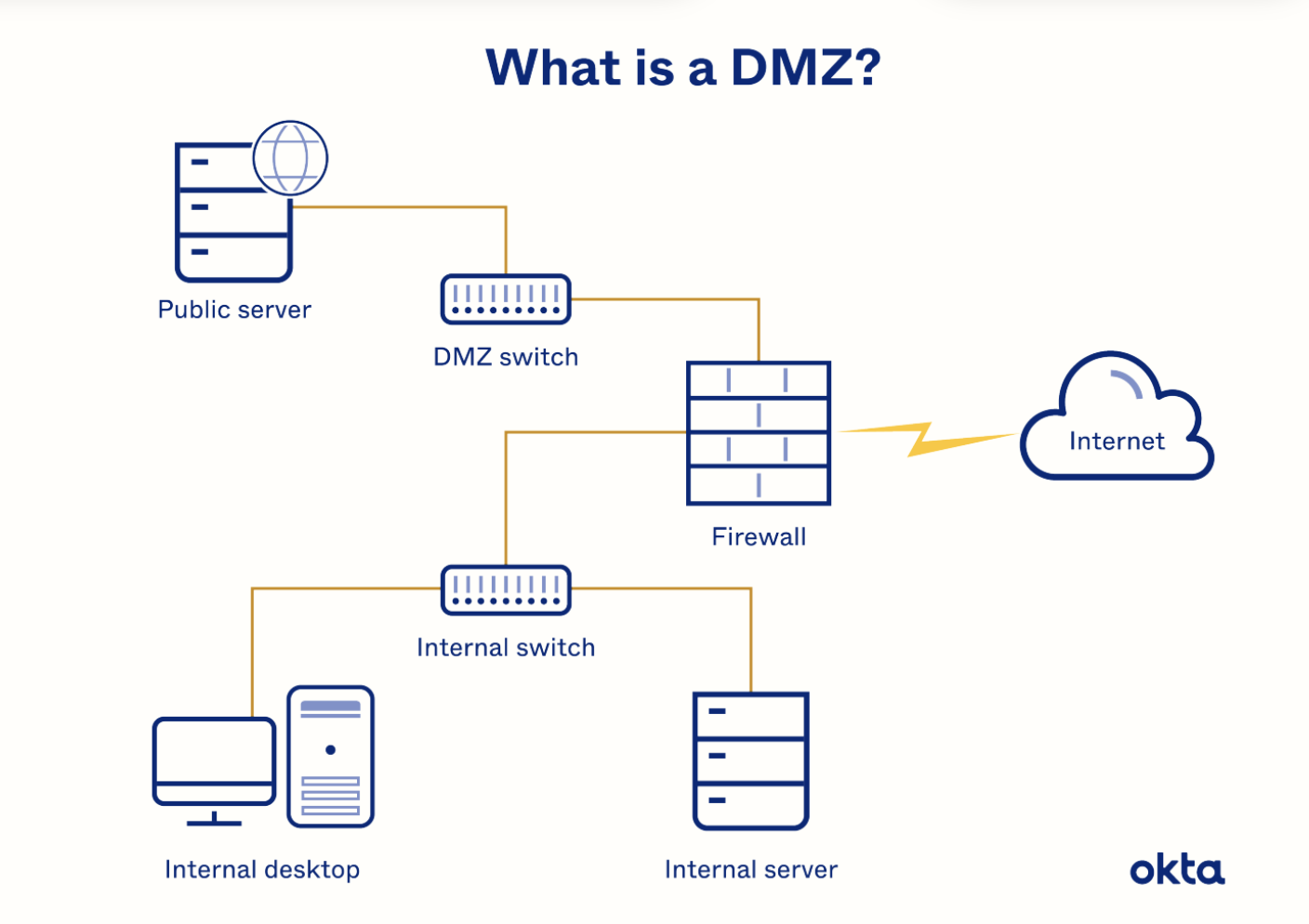
4. Proposed Architecture Overview
Explain layers in plain language:
- Public access server (in DMZ)
- Application processing server (internal)
- Secure database server (isolated)
- Controlled communication between layers
No technical ports. No jargon.
5. Security Benefits
- Network isolation
- Limited exposure to the Internet
- Strict firewall rules
- Controlled internal access
- Regular backups
- Audit capability
Translate everything into risk reduction language.
6. Risks & Mitigation
| Risk | Mitigation | |Hardware failure | RAID + backup server | |Cyber attack | DMZ isolation + firewall | | Data loss | Daily backups | | Human error | Access control + logging
7. Cost Considerations
Explain clearly:
- Initial hardware investment
- Maintenance effort
- Electricity / cooling
- IT administration
- No recurring cloud subscription fees
8. Roadmap (High Level)
- Phase 1: Infrastructure setup
- Phase 2: Application deployment
- Phase 3: Security hardening
- Phase 4: Go-live
- Phase 5: Monitoring & optimization
9. Decision Points Needed from Stakeholders
This is critical.
Examples:
- Approval for hardware budget
- Approval for network configuration
- Security policy alignment
- Disaster recovery expectations