Sample DMZ Network Architectures
Any network implementing a DMZ (Demilitarized Zone) must use firewalls to separate public-facing services from internal systems.
There are two primary architectural models:
- Single Firewall DMZ
- Dual Firewall DMZ
Each provides a different level of isolation and security control.
1. Single Firewall DMZ Network
Overview
A single firewall DMZ uses one physical firewall device with multiple network interfaces to segment traffic between:
- Internet (Untrusted Zone)
- DMZ (Semi-trusted Zone)
- Internal LAN (Trusted Zone)
Core Components
Firewall
- First and only security boundary.
- Must have at least three interfaces (WAN, DMZ, LAN).
- Enforces all traffic rules between zones.
Switches
- DMZ switch: connects public-facing servers.
- Internal switch: connects application and internal servers.
Servers
- Public servers in the DMZ (e.g., web server, reverse proxy).
- Private servers in the internal LAN (e.g., application server, database).
Logical Structure
Internet
│
Firewall (3 interfaces)
├── DMZ → Public Servers
└── LAN → Internal ServersSecurity Characteristics
- All segmentation depends on one firewall.
- Access control is rule-based.
- Internal systems are protected from direct internet exposure.
- DMZ systems cannot access LAN resources unless explicitly allowed.
Advantages
- Lower cost
- Simpler configuration
- Easier maintenance
- Suitable for small to medium environments
Risks / Limitations
- Single point of failure
- If firewall is compromised, segmentation collapses
- Rule misconfiguration can expose internal services
When Appropriate
- Moderate security requirements
- Controlled user base
- Budget-sensitive deployments
- Non-critical public services
2. Dual Firewall DMZ Network
Overview
A dual firewall architecture uses two separate firewalls to create layered protection between:
- Internet
- DMZ
- Internal LAN
This model provides stronger isolation and defense-in-depth.
Core Components
Perimeter Firewall (External Firewall)
- Filters traffic from the Internet to the DMZ.
- Allows only required public services (e.g., HTTPS).
Internal Firewall
- Controls traffic between the DMZ and the LAN.
- Protects sensitive systems (databases, internal apps).
DMZ
- Hosts public services (web servers, reverse proxies, mail gateways).
LAN
- Hosts private services (application servers, databases, internal tools).
Logical Structure
Internet
│
Perimeter Firewall
│
DMZ (Public Servers)
│
Internal Firewall
│
LAN (Application + Database)Security Characteristics
- Two independent security layers.
- Even if a DMZ server is compromised, attacker must bypass second firewall.
- Strong separation of trust zones.
Advantages
- Higher security
- Better containment of breaches
- Clear separation of responsibilities
- Suitable for regulated environments
Risks / Considerations
- Higher cost
- More complex configuration
- Requires coordinated firewall rule management
- Increased operational overhead
When Appropriate
- Sensitive data environments
- Regulatory compliance requirements
- Public-facing critical systems
- Higher threat exposure
3. Extended Security Models
Classified / Controlled Militarized Zone (CMZ)
In high-security environments, organizations may introduce an additional isolated zone (sometimes referred to as a CMZ).
This structure adds another segmentation layer for:
- Highly sensitive application gateways
- Monitoring systems
- Security inspection tools
- Reverse proxies
Example Structure
Internet
│
Firewall
│
DMZ (Public Edge Services)
│
CMZ (Controlled Services)
│
Internal Firewall
│
LAN (Core Systems)
This model increases isolation but also operational complexity.
Comparison Summary
|Architecture | Security Level| Complexity |Cost |Typical Use | |Single Firewall| Moderate| Low |Low| SMEs, internal platforms| |Dual Firewall | High| Medium| Medium–High |Enterprise, regulated systems| |CMZ Model| Very High| High| High |Critical infrastructure|
Recommendation (Preliminary)
For an on-premises deployment hosting application and database servers:
- Use Dual Firewall Architecture if:
- Data sensitivity is high
- External exposure is required
- Long-term scalability is expected
- Use Single Firewall Architecture only if:
- Infrastructure is small
- Risk profile is moderate
- Budget constraints are significant
Use Case Example
DMZ Network Architecture for Inspection Questionnaire System
Context
The system supports:
- Offline questionnaire data collection (mobile / PWA)
- Secure synchronization when connection is available
- Centralized storage of inspection data
- Internal processing and report generation
- Restricted access to sensitive vessel and inspection records
The architecture must ensure:
- No direct internet access to the database
- Controlled API exposure
- Segmented trust zones
- Data integrity and auditability
1. Dual Firewall DMZ (Recommended Model)
Structure
Internet
│
Perimeter Firewall
│
DMZ (Reverse Proxy / API Gateway)
│
Internal Firewall
│
LAN (Application + Database + Internal Tools)
Component Mapping to Inspection System
Perimeter Firewall
- Allows HTTPS (443) only.
- Blocks all other inbound traffic.
- Prevents direct LAN access.
DMZ
- Reverse Proxy
- API Gateway
- Optional Web Application Firewall (WAF)
- No persistent inspection data stored here.
Internal Firewall
- Allows only specific traffic from DMZ to:
- Application server API port
- Blocks lateral movement.
- Prevents DMZ → Database direct access.
LAN
- Application Server
- Database Server
- Backup Server
- Report generation engine
- Internal admin dashboard
Traffic Flow (Inspection Sync Scenario)
- Inspector completes questionnaire offline.
- Device connects to public HTTPS endpoint.
- Perimeter firewall filters traffic.
- Reverse proxy validates request.
- Internal firewall permits only API traffic to application server.
- Application validates payload.
- Data written to database.
- Audit log created.
At no point:
- Does the database accept external traffic.
- Does DMZ contain core inspection data.
2. Security Relevance for Inspection Data
Inspection data may include:
- Vessel information
- Operational compliance findings
- Remarks and photographic evidence
- Internal clearance notes
This information can be commercially sensitive.
Therefore:
- Database must remain fully isolated.
- Application logic must reside internally.
- Public-facing layer must be stateless.
- Backup server must not be in DMZ.
3. Optional Hardening Layer (High-Sensitivity Scenario)
For higher assurance:
- Add a dedicated Backup VLAN.
- Restrict database access to application server IP only.
- Enforce mutual TLS between DMZ and application server.
- Implement network-level logging and intrusion detection.
Structure:
Internet
│
Perimeter Firewall
│
DMZ
│
Internal Firewall
│
Application VLAN
│
Database VLAN
│
Backup VLAN4. Architectural Recommendation for This Project
Given the system characteristics:
- Offline-first inspectors
- Central synchronization
- Sensitive compliance data
- Long-term scalability expectations
Recommended model:
→ Dual Firewall DMZ
→ Dedicated internal database isolation
→ No direct public database exposure
→ Stateless DMZ layerThis ensures:
- Containment of potential web-layer compromise
- Clear separation of responsibilities
- Enterprise-grade posture without cloud dependency
- Scalability for future modules (CRM, clearance management, reporting)
- Decision Framing for Stakeholders Meeting
If stakeholders ask:
“Why not a simpler setup?”
Answer:
- Inspection data has long lifecycle value.
- A breach impacts trust and commercial credibility.
- Dual firewall adds structural protection, not just software protection.
- Architecture should match data sensitivity, not current size.
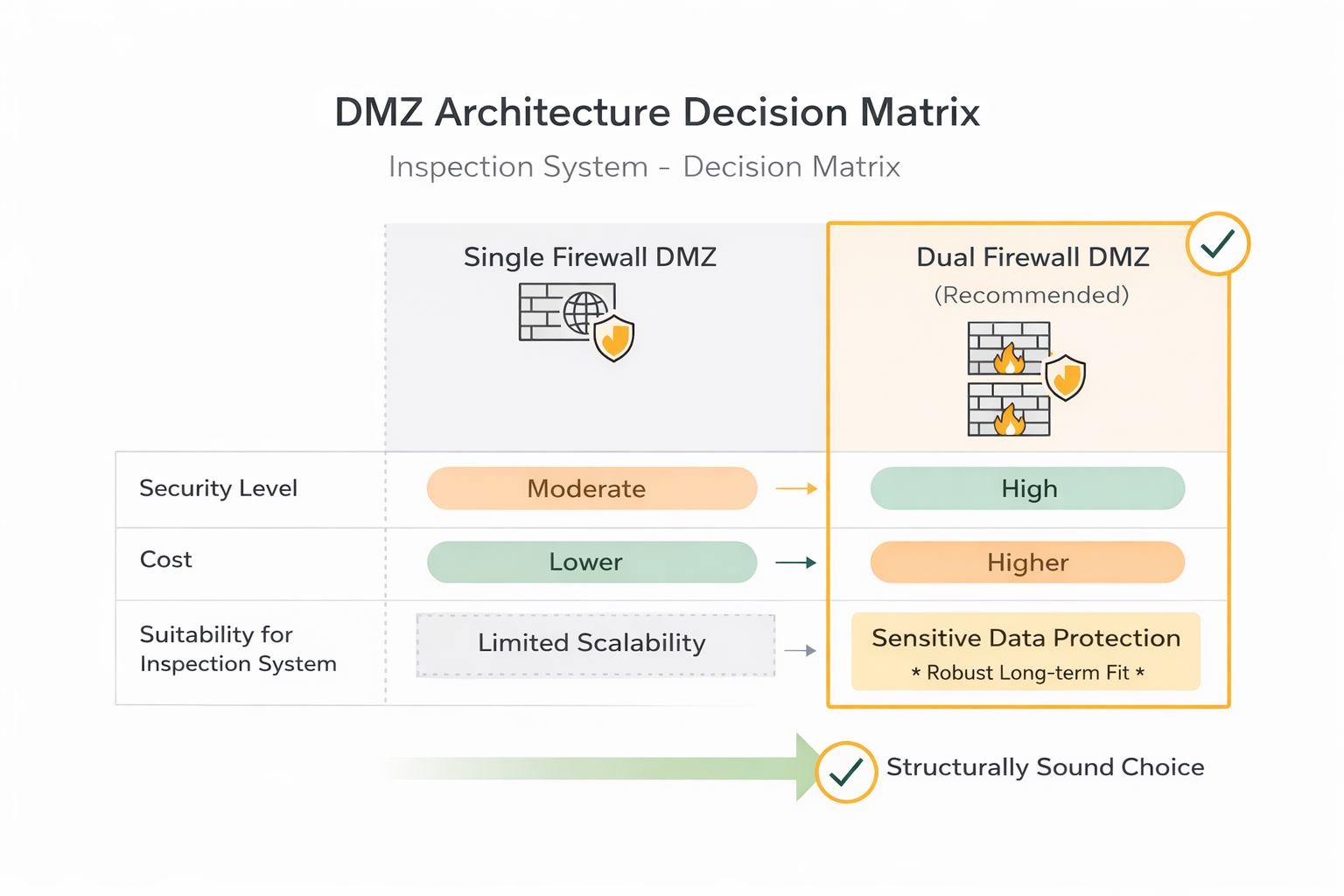
Visual Decision Matrix Diagram
On-Premises Dual Firewall DMZ Minimum Hardware
Architecture Overview
Internet ↓ Perimeter Firewall ↓ DMZ (Reverse Proxy) ↓ Internal Firewall ↓ Application Server ↓ Database Server ↓ Backup Server
Minimum Hardware Components
- Perimeter Firewall
- 4 cores CPU
- 4–8 GB RAM
- 3 network interfaces
- Dual PSU (recommended)
Purpose: Internet filtering, HTTPS exposure only
- Internal Firewall
- 4 cores CPU
- 4–8 GB RAM
- 3 network interfaces
Purpose: Strict DMZ → LAN segmentation
- DMZ Server (Reverse Proxy)
- 4 cores CPU
- 8 GB RAM
- 250 GB SSD
Purpose: TLS termination, API gateway, stateless layer
- Application Server
- 8 cores CPU
- 16 GB RAM
- 500 GB SSD
Purpose: Business logic, validation, reporting
- Database Server (Critical Component)
- 8 cores CPU
- 32 GB RAM
- SSD RAID 1 (OS)
- SSD RAID 1 (Data)
Purpose: Inspection data, photos, audit logs
- Backup Server (Strongly Recommended)
- 4 cores CPU
- RAID storage (capacity ≥ 3× annual growth)
Purpose: Nightly backups, disaster recovery
Network Requirements
- Managed switch with VLAN support
- Minimum VLANs:
- DMZ
- Application LAN
- Database VLAN
- Static public IP
- 50–100 Mbps internet sufficient
Estimated Data Growth
For mid-complexity inspections:
- nnn–nnn inspections/year
- Photos are primary storage driver
- Estimated growth: 50–150 GB/year
Plan storage for 3–5 years minimum.
What This Provides
- Layered protection (dual firewall)
- Full database isolation
- No direct internet database exposure
- Scalability for future modules
- Enterprise-grade security posture
- 3–5 year lifecycle stability
Executive Summary
Minimum secure deployment requires:
- 2 firewalls
- 3 core servers (DMZ / App / DB)
- 1 backup server
- VLAN-capable network
This is the structurally sound baseline for protecting sensitive inspection data under a mid-complexity environment.